🌐 STTI1
A detailed write-up of the Web challenge 'STTI1' from PicoCTF - 2025
📊 Challenge Overview
Category Details Additional Info 🏆 Event PicoCTF - 2025 Event Link 🔰 Category Web 🌐 💎 Points 100 Out of 500 total ⭐ Difficulty 🟢 Easy Personal Rating: 1/10 👤 Author Venax Profile 🎮 Solves (At the time of flag submission) 1.576 solve rate 📅 Date 10-03-2025 PicoCTF - 2025 🦾 Solved By mH4ck3r0n3 Team:
📝 Challenge Information
I made a cool website where you can announce whatever you want! Try it out! I heard templating is a cool and modular way to build web apps! Check out my website here!
🎯 Challenge Files & Infrastructure
Provided Files
1Files: None
🔍 Initial Analysis
First Steps
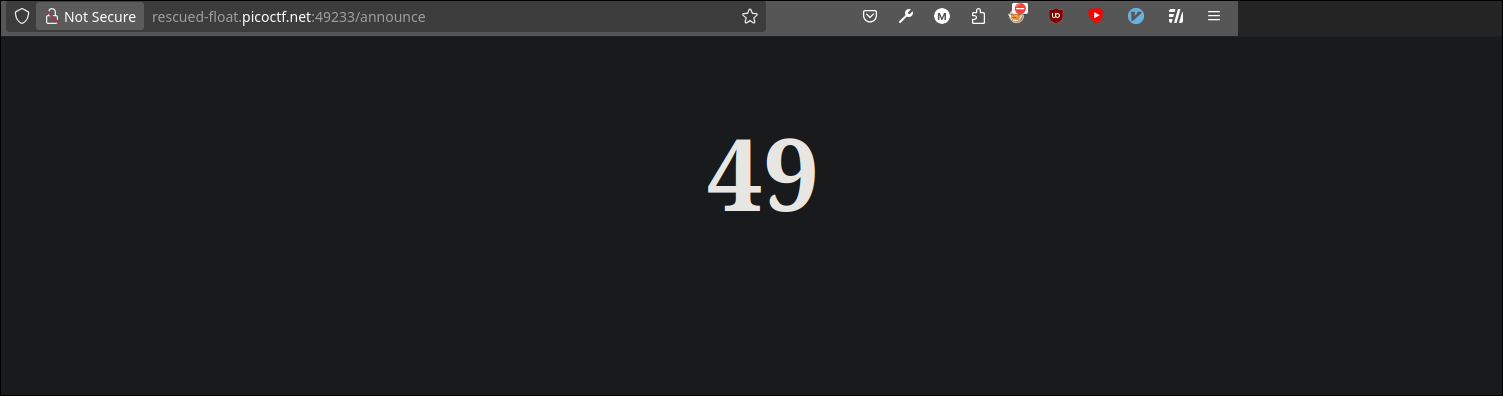
Initially, the website appears as follows:
As the title suggests, it is most likely a
SSTI (Server Side Template Injection), so I immediately decided to try withJinja2, since it is the most common, by injecting{{ 7*7 }}:As we can see, the template is rendered, and we have an
SSTI. Let’s proceed to the exploitation phase.
🔬 Vulnerability Analysis
Potential Vulnerabilities
- STTI (Server Side Template Injection)
🎯 Solution Path
Exploitation Steps
Initial setup
Now we just need to find the object chain to reach
osorsubprocess. I tried some standard ones from HackTricks. Let’s move on to the exploitation phase.
Exploitation
By testing a couple of payloads, I found one that worked in this case and did not generate an
Internal Server Error:{{config.__class__.__init__.__globals__['os'].popen('ls').read()}}. When I sent it through theinputbox, I successfully executed thelscommand:As we can see, there is a
flagfile. So, I modified the payload to:{{config.__class__.__init__.__globals__['os'].popen('cat flag').read()}}to executecat flag. After sending it, I successfully retrieved the flag.
Flag capture
🛠️ Exploitation Process
Approach
The automatic exploit performs the same steps as the manual exploit, sending the
SSTIpayload with a POST request and extracting the flag from the response using a regex.
🚩 Flag Capture
Flag
Proof of Execution
🔧 Tools Used
Tool Purpose Python Exploit
💡 Key Learnings
Skills Improved
- Binary Exploitation
- Reverse Engineering
- Web Exploitation
- Cryptography
- Forensics
- OSINT
- Miscellaneous
📚 References & Resources
Learning Resources
📊 Final Statistics
| Metric | Value | Notes |
|---|---|---|
| Time to Solve | 00:03 | From start to flag |
| Global Ranking (At the time of flag submission) | 2609/8397 | Challenge ranking |
| Points Earned | 100 | Team contribution |
Created: 10-03-2025 • Last Modified: 10-03-2025 *Author: mH4ck3r0n3 • Team: *