🌐 N0s4n1ty 1
A detailed write-up of the Web challenge 'N0s4n1ty 1' from PicoCTF - 2025
📊 Challenge Overview
Category Details Additional Info 🏆 Event PicoCTF - 2025 Event Link 🔰 Category Web 🌐 💎 Points 100 Out of 500 total ⭐ Difficulty 🟢 Easy Personal Rating: 2/10 👤 Author Prince Niyonshuti N. Profile 🎮 Solves (At the time of flag submission) 1.580 solve rate 📅 Date 19-03-2025 PicoCTF - 2025 🦾 Solved By mH4ck3r0n3 Team:
📝 Challenge Information
A developer has added profile picture upload functionality to a website. However, the implementation is flawed, and it presents an opportunity for you. Your mission, should you choose to accept it, is to navigate to the provided web page and locate the file upload area. Your ultimate goal is to find the hidden flag located in the /root directory.
🎯 Challenge Files & Infrastructure
Provided Files
1Files: None
🔍 Initial Analysis
First Steps
Initially, the website appears as follows:
It is a web application that allows us to change the profile picture. By reading the URL, I noticed that it is
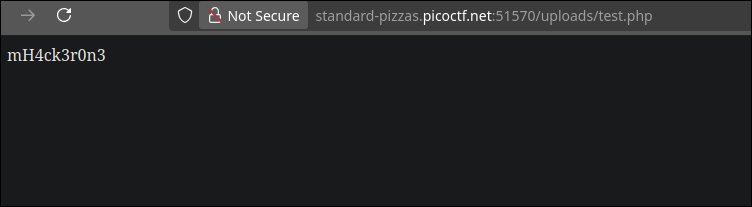
php. So, I immediately thought, “What if I upload a php file?”. I created a.phpfile withecho "mH4ck3r0n3";inside and uploaded it. Once the file was uploaded, I was redirected to a page saying that the filetest.phpwas uploaded to the/uploadsdirectory. So, I visited the page/uploads/test.php:Realizing that the
phpwas indeed executed. Now that we understand the vulnerability, let’s move on to the next phase.
🔬 Vulnerability Analysis
Potential Vulnerabilities
- RCE (Remote Code Execution)
🎯 Solution Path
Exploitation Steps
Initial setup
The first thing I did was immediately write a
php reverse shell(https://www.revshells.com/). I copied the reverse shell:php cmdand saved it asphp-reverse-shell.php. Let’s move on to the next phase.
Exploitation
Just like with the test file, I uploaded the
php-reverse-shell.phpfile:And by visiting
/uploads/php-reverse-shell.php, I got my reverse shell. Now, as mentioned in the challenge description, we need to read theflag.txtfile located in the/rootdirectory. The first thing I did was runls -la /:This allowed me to see the permissions on the
/rootdirectory, and since I discovered that I am thewww-datauser withwhoami, we can see that I don’t have the necessary permissions to access/root. Since I don’t think this is a privilege escalation challenge, I ransudo -lto check the permissions associated with my user:And as we can see, no password is required to use the
sudocommand. So, I tried accessing/rootto see its contents by runningsudo ls /root:And as we can see, I was able to access it, and inside there’s only the
flag.txtfile. So, I ransudo cat /root/flag.txtto read the contents of the file and consequently retrieve the flag.
Flag capture
🛠️ Exploitation Process
Approach
The automated exploit generates the reverse shell, performs the upload, and executes
sudo cat /root/flag.txt, then extracts the flag using a regex.
🚩 Flag Capture
FlagpicoCTF{wh47_c4n_u_d0_wPHP_b42a374d}
Proof of Execution
🔧 Tools Used
Tool Purpose Python Exploit
💡 Key Learnings
Time Optimization
- As soon as you have a reverse shell, the first thing you should always do is sudo -l.
Skills Improved
- Binary Exploitation
- Reverse Engineering
- Web Exploitation
- Cryptography
- Forensics
- OSINT
- Miscellaneous
📚 References & Resources
Learning Resources
📊 Final Statistics
| Metric | Value | Notes |
|---|---|---|
| Time to Solve | 00:05 | From start to flag |
| Global Ranking (At the time of flag submission) | 1339/10460 | Challenge ranking |
| Points Earned | 100 | Team contribution |
Created: 19-03-2025 • Last Modified: 19-03-2025 *Author: mH4ck3r0n3 • Team: *